Accessing Services with Verifiable Credentials

Access Overview
The Access experience pattern leverages digital credentials to simplify and secure the way users access services online or in-person. By utilizing digital credentials stored in a digital wallet, users can seamlessly prove their identity or attributes without relying on traditional usernames and passwords or physical IDs. This approach enhances user convenience and strengthens security across various digital interactions.
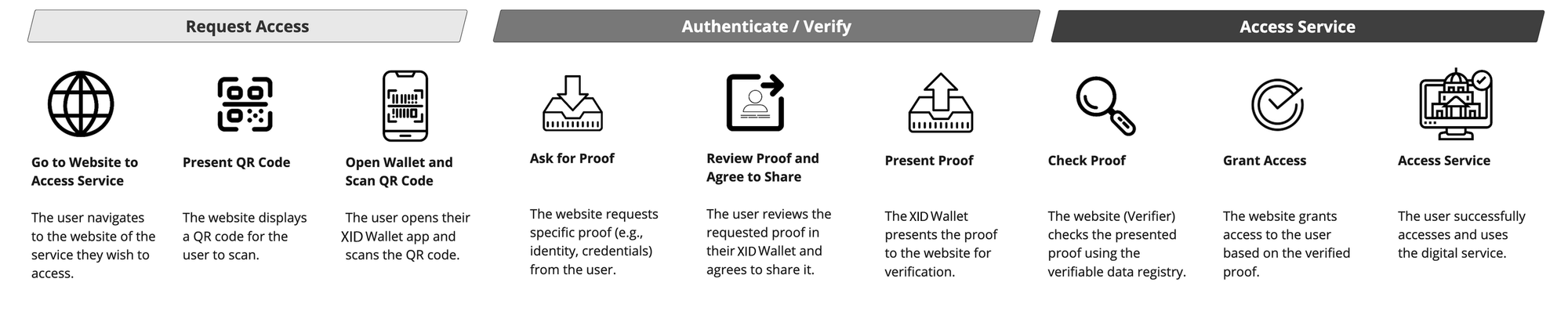
How it works Digital Trust Access enables users to securely and seamlessly access services online or in person using verifiable digital credentials. The process involves three key steps: Request, Verify, Access.
Request: The user initiates the process by navigating to the service website and scanning a QR code using their Xanadu ID Wallet.
Verify: The service requests proof of identity or credentials, which the user reviews and shares through their Xanadu ID Wallet.
Access: The service validates the credentials via the verifiable data registry and grants the user access to the digital service.
Technology Required:
- Xanadu ID Wallet: A secure digital wallet application for storing and managing digital credentials.
- Digital credential(s): A cryptographically secure and verifiable proof of identity or attributes.
- Your digital service: The service being accessed, which relies on digital credentials for authentication.
Benefits
Problem: Traditional access methods, such as usernames and passwords, present significant security vulnerabilities and are often cumbersome for people. These methods are prone to data breaches, phishing attacks, and require extensive management for password recovery and updates.
Benefits: Digital credentials address these issues by providing a more secure and user-friendly authentication method. They offer cryptographic assurance, reducing the risk of data breaches and identity theft. Additionally, digital credentials streamline the access process, improving the overall user experience and aligning with best practices in digital identity management.
Suitable use cases
The Xanadu offers a variety of solutions for accessing services online or in person, with digital trust and credentials emerging as innovative methods to enhance and complement existing systems. Digital trust solutions provide flexible and secure access, making them suitable for a range of applications.
Consider Digital Trust If:
- New or Existing Services: Digital trust is valuable for both new and existing services, providing secure access and extending into other experiences like signing, issuing, and messaging through Xanadu ID wallet app.
- Leveraging Existing Credentials: There are existing digital credentials that can be integrated into your service. If your service requires the issuance of a new credential, that is also possible.
- Team and Buy-in: Your organization has the appropriate team and buy-in to lead the adoption of digital trust, ideally agile teams with an appetite for experimentation and innovation.
Technology stacks
There are different digital credential authentication solutions your digital service can leverage.
| Description | VC-AuthN & Pathfinder SSO | Xanadu Traction | Xanadu ID Wallet Verify feature |
|---|---|---|---|
| Description | Verifiable Credential Authentication via OpenID Connect (VC-AuthN) is ready made using a standardized system | Xanadu Traction is a customizable digital wallet solution that can both issue, hold and verify digital credentials | Mobile verifier is a feature within the Xanadu ID Wallet app that can authenticate people in-person |
| Devices | Used on web and mobile | Can integrate with web and mobile applications | Used on mobile only |
| Implementation requirements | - Quick to implement, integrates easily with current web standards. - May require manual management of user roles/permissions, especially if the proof request does not contain any identifiers for returning people. |
Requires more time and resources to set up as well as ongoing maintenance | - Quick and easy to set up. No implementation required. - Requires manual human verification. |
| Customization | Low - Can use existing and customize proof requests | High- Can customize flows to meet your needs | Low - Can use existing and customize proof requests |
| Suitability | - Your service already or easily supports OpenID Connect - Quicker turnaround - Your access requirements require only a single proof request |
Your service needs to scale and integrate with different organizations and services | - Quicker turnaround - Your access requirements require only a single proof request |
| Capabilities | Can leverage existing proof requests and digital credentials | Can issue, hold, and verify digital credentials | - In-person verification - No development resources needed |
Traction Sequence Diagram Example
The following sequence diagram visualizes the Access pattern using digital credentials using Traction. It demonstrates the process of a person (Holder) accessing a service (Verifier) with a digital credential issued in their Xanadu wallet.
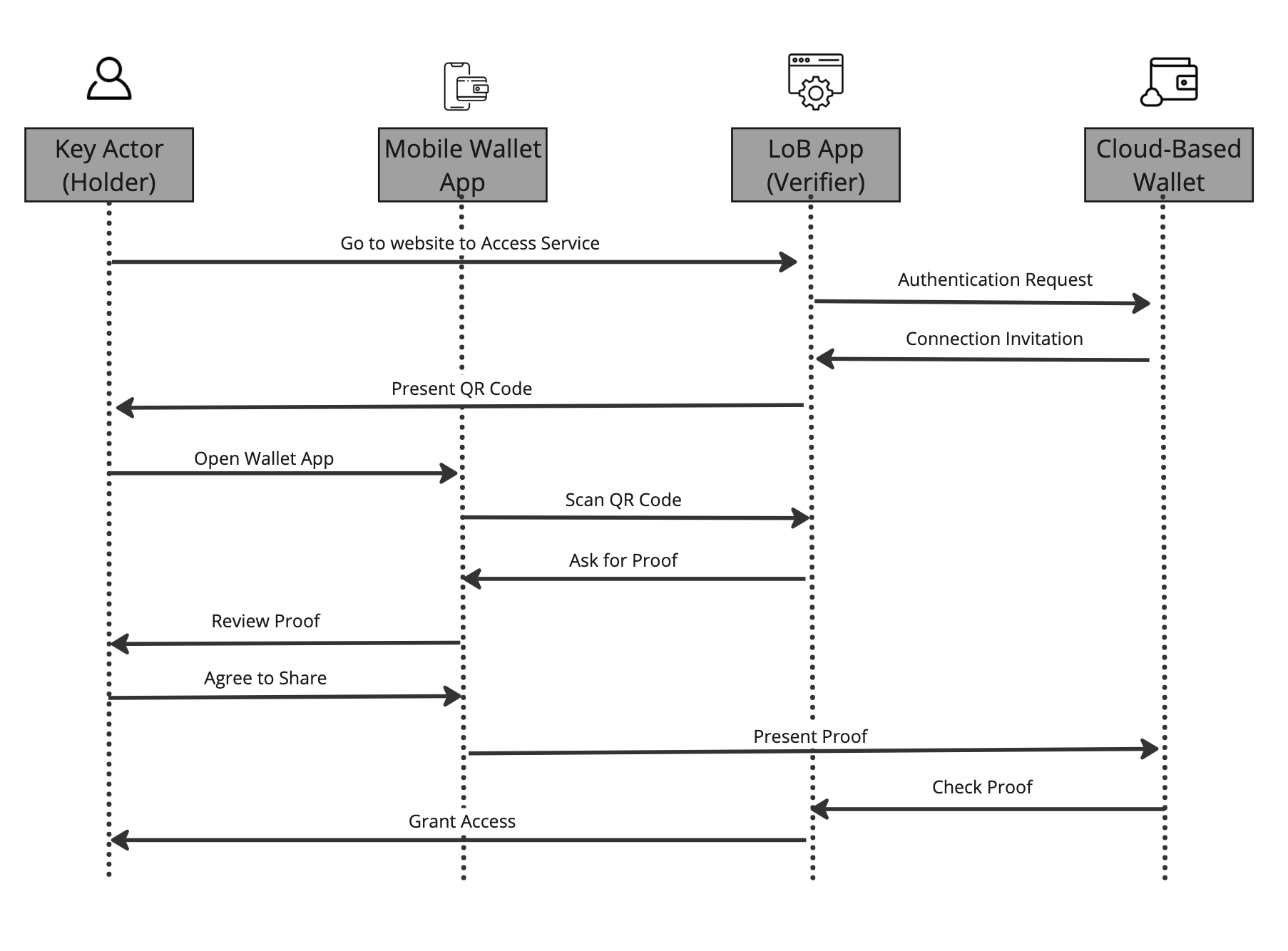
Source: Digital Trust Toolkit